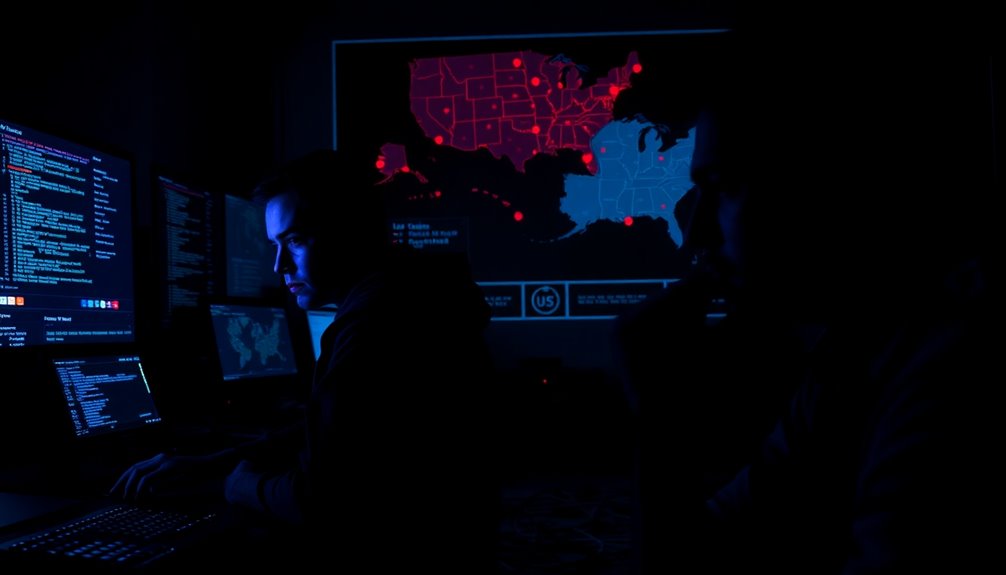
As Russia intensifies its sabotage efforts targeting key sectors like transportation and critical infrastructure, the threat to U.S. interests both abroad and at home grows more urgent. You might feel the unease as you consider how these operations, conducted by Russian intelligence services like the GRU and FSB, not only disrupt commerce but also pose significant security risks. Their goal is clear: undermine Western support for Ukraine by targeting companies involved in weapon production and shipment. This tactic creates a ripple effect, impacting your economic stability and safety.
Despite the pressing nature of these threats, you’ll notice that the U.S. response has often held back, particularly in the realm of cyber defenses. While the U.S. Cyber Command has conducted offensive operations to counteract Russian cyber threats, there have been reports of temporary halts. It’s a delicate balance. NATO countries face challenges in responding effectively without escalating the situation into a conventional war. So, it’s understandable why the U.S. might tread cautiously. Russia’s aggressive tactics have forced Western nations to reconsider their approach to cybersecurity.
You may also recognize the importance of international cooperation in this context. As U.S. and European agencies collaborate, they can better anticipate and mitigate these threats. Enhanced cybersecurity measures are crucial, especially considering the sophisticated tactics employed by Russian cyber actors like those involved in the SolarWinds breach. These actors use highly targeted spear-phishing campaigns to penetrate government and defense sectors, causing you to wonder about the vulnerability of even the most secure systems. Regular security training can significantly enhance awareness and preparedness.
In your workplace or community, enhanced security measures can make a difference. Regular training and awareness programs are vital for employees to recognize potential threats. Establishing robust incident response protocols can help mitigate the impact of sabotage if it occurs. You’ll want to prioritize your critical assets, ensuring that your security efforts are focused where they matter most.
While the U.S. grapples with its response, the international landscape remains complex. You can feel the weight of the challenge as NATO plays a significant role in coordinating efforts against these sabotage operations. The need for a comprehensive regulatory framework becomes evident; existing legal structures guide how the U.S. can effectively respond without triggering a larger conflict.
In this precarious situation, the urgency to bolster cyber defenses is clear. By staying informed and engaged, you can contribute to a more secure environment amidst the lurking threats of Russian sabotage.

Cybersecurity Essentials for Business Leadership
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Norton Personal Firewall 2005 – Single User
- User-friendly security software: Protects against hackers and thieves
- Intrusion prevention technology: Adds extra security layer
- Data protection feature: Blocks unauthorized info sharing
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

ASUS RT-AX1800S Dual Band WiFi 6 Extendable Router, Subscription-Free Network Security, Parental Control, Built-in VPN, AiMesh Compatible, Gaming & Streaming, Smart Home
- WiFi Standard: WiFi 6 (802.11ax) with MU-MIMO & OFDMA
- WiFi Speed: Supports 1024-QAM for faster connections
- Device Capacity: Supports multiple devices simultaneously
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.