White noise machines are used in private offices to create a steady…
Browsing Category
Explainers
157 posts
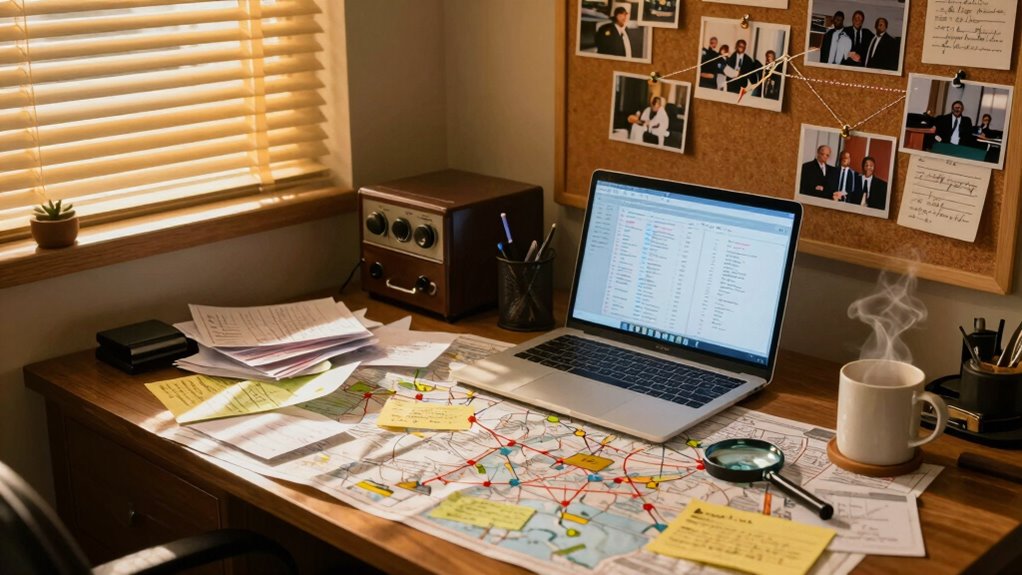
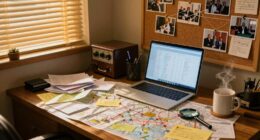
What the Intelligence Cycle Looks Like in Real Life
What the intelligence cycle looks like in real life reveals a continuous process that shapes critical decisions—discover how each step impacts real-world outcomes.
What Cable Testers Reveal About Network Problems
Narrowing down network issues, cable testers reveal faults and interference, but understanding their full potential can unlock better connectivity—discover how inside.
How Voice Cloning Technology Can Be Used in Espionage
Of all espionage tools, voice cloning reveals surprising capabilities that could change covert operations forever—discover the full scope if you dare to explore.
Why Spy Agencies Care About Cryptocurrency Flows
National security agencies monitor cryptocurrency flows to prevent criminal activities, but their evolving techniques reveal surprising insights into covert financial operations.
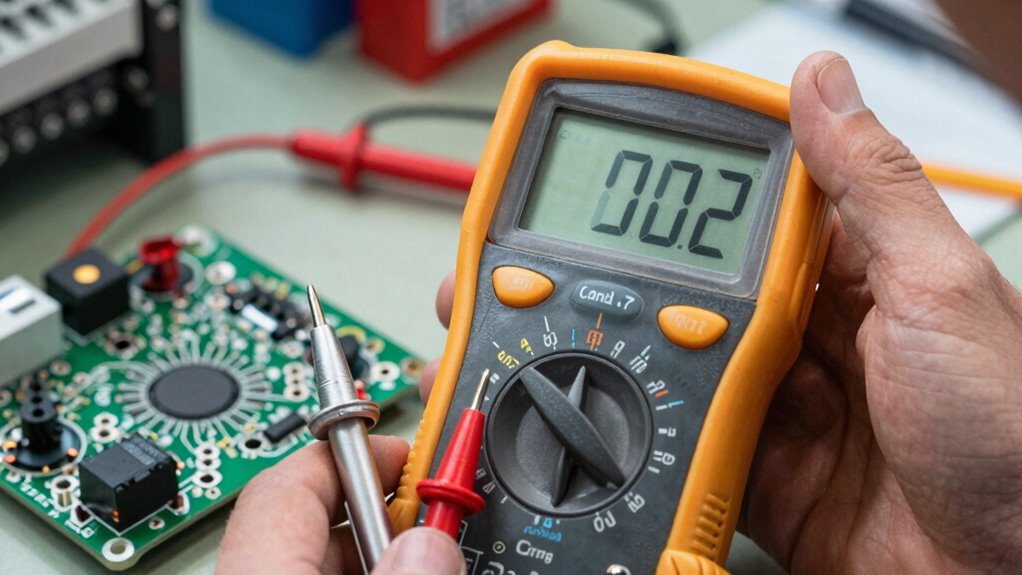
Why Professional Multimeters Remain Essential Tools
Discover why professional multimeters are essential tools and how they can elevate your electrical work—continue reading to find out more.
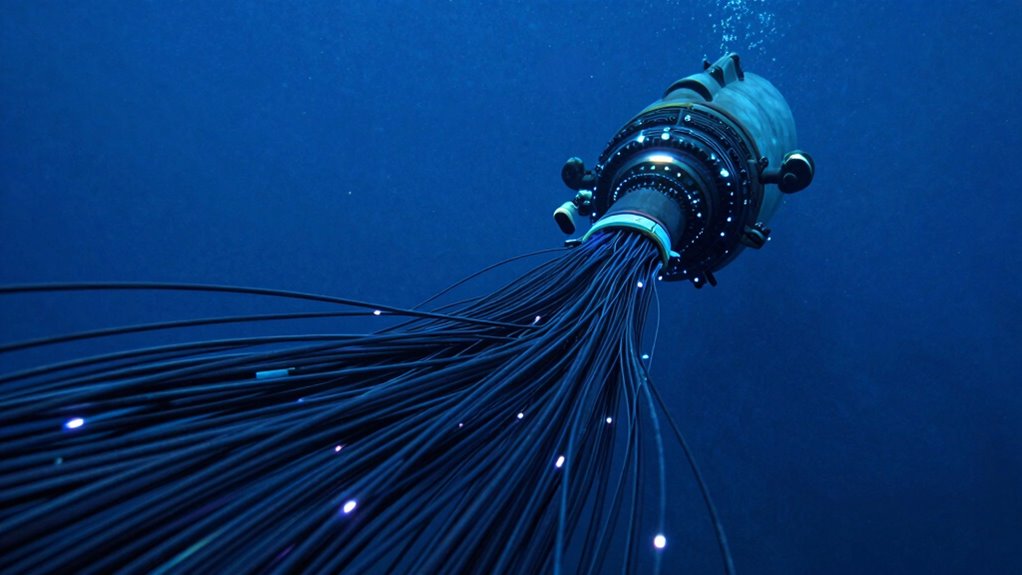
How Undersea Cable Interception Became a Strategic Priority
Keenly understanding undersea cable interception reveals its rise as a strategic priority, but the true implications are just beginning to unfold.
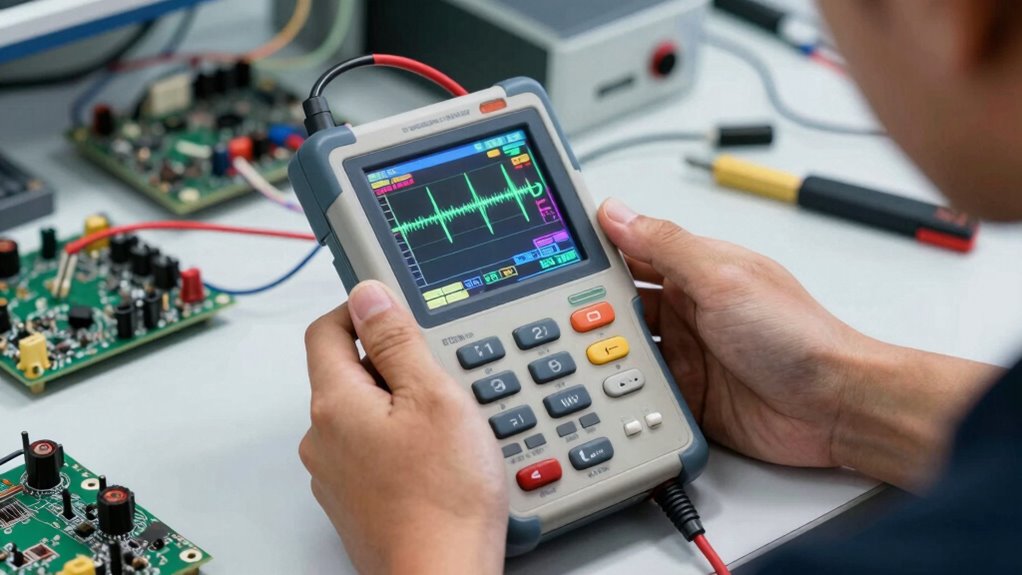
How Handheld Oscilloscopes Help With Quick Diagnostics
Probing electronic issues swiftly, handheld oscilloscopes offer portability and precision, transforming troubleshooting—discover how they simplify diagnostics today.
What Cell-Site Simulators Do and Why They Are Controversial
A detailed look at how cell-site simulators track your location and communications, raising privacy concerns that demand further investigation.
What Spectrum Analyzers Measure in Plain English
Spectrometers measure the frequencies and strengths of signals, revealing hidden details and helping you understand what’s really going on behind the noise.