TL;DR
Cybersecurity researchers have estimated that the largest malware repositories amount to tens of thousands of hard drives, reaching heights comparable to iconic landmarks. This highlights the vast scale of malware data collected and stored by security firms.
Research indicates that the largest malware repositories, such as vx-underground’s 30 terabytes and VirusTotal’s 31 petabytes of data, are enormous enough to be visualized as stacks of hard drives reaching heights comparable to iconic landmarks like the Eiffel Tower and Burj Khalifa.
Malware research group vx-underground reports having approximately 30 terabytes of malware source code, while VirusTotal, a widely used online scanning service, states it has about 31 petabytes of malware samples contributed by users. To illustrate the scale, researchers performed calculations assuming standard 1-terabyte hard drives, each about 1 inch tall, to estimate the physical height of these data collections.
According to these estimates, vx-underground’s 30 terabytes would fill roughly 30 hard drives stacked vertically, reaching about 2.5 feet tall—roughly the height of a typical person. In contrast, VirusTotal’s 31 petabytes would require approximately 31,744 hard drives, stacking up to about 2,645 feet, or roughly the height of the Burj Khalifa in Dubai. This means VirusTotal’s malware archive is comparable in height to two and a half Eiffel Towers stacked vertically.
Why It Matters
This comparison underscores the enormous volume of malware data collected by cybersecurity firms, which is instrumental for training detection models and understanding evolving threats. The sheer size of these repositories reflects the scale of malicious activity and the ongoing efforts required to combat cyber threats globally.

Seagate Portable 1TB External Hard Drive HDD – USB 3.0 for PC, Mac, PlayStation, & Xbox, 1-Year Rescue Service (STGX1000400) , Black
- Storage Capacity: 1TB portable external hard drive
- Compatibility: Works with Windows and Mac
- Easy Backup: Drag-and-drop file transfer
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Background
Both vx-underground and VirusTotal are key players in malware research and threat intelligence. vx-underground claims to have the largest collection of malware source code, while VirusTotal aggregates malware samples from users worldwide. These repositories are critical for cybersecurity research, AI training, and threat analysis. The comparison of their sizes to physical landmarks offers a tangible perspective on the data volume involved, which has grown significantly over recent years amid increasing cyber threats.
“The scale of these malware repositories is staggering, reaching heights comparable to iconic landmarks like the Eiffel Tower and Burj Khalifa, illustrating the vast amount of malicious data security firms handle.”
— Zack Whittaker, TechCrunch security editor
“Estimating the physical height of these datasets helps us grasp just how massive these repositories are and the challenge they present for cybersecurity efforts.”
— Unattributed researcher
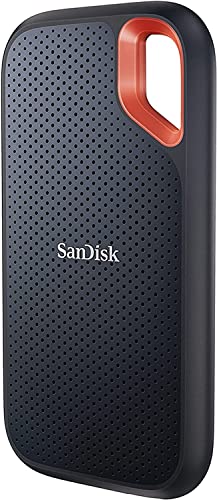
SANDISK 4TB Extreme Portable SSD (Old Model) – Up to 1050MB/s, USB-C, USB 3.2 Gen 2, IP65 Water and Dust Resistance, Updated Firmware – External Solid State Drive – SDSSDE61-4T00-G25
- High-speed Data Transfer: Up to 1050MB/s read, 1000MB/s write
- Durable and Water-resistant: IP65 water and dust resistance, 3-meter drop protection
- Portable and Secure: Includes carabiner loop for easy attachment
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
What Remains Unclear
These calculations are rough estimates based on assumed hard drive sizes and do not account for data compression, storage efficiencies, or actual physical storage formats. The exact physical arrangement of these datasets remains unknown, and the comparison is primarily illustrative.

PNY 256GB Attaché X USB 3.2 Gen 1 Flash Drive, Advanced Performance Up to 130MB/s Read, Everyday Data Store & Transfer, Reliable Portable Storage, Durable, Type-A, Computers, Laptops, Desktops
- High-speed Data Transfer: Up to 130MB/s read speed
- Fast Transfer Rates: Up to 10x faster than USB 2.0
- Durable Design: Lightweight with sliding collar cap
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
What’s Next
Further analysis may involve detailed mapping of storage infrastructure for these datasets. As malware repositories continue to grow, cybersecurity firms will need to develop more scalable storage and analysis solutions. Ongoing research will also aim to quantify the impact of such large datasets on threat detection and response capabilities.

MAIWO Hard Drive RAID Enclosure Dual Bay for 2.5 Inch SATA SSD HDD, USB 3.1 GEN 2 10Gbps with UASP, RAID 0/1/JBOD/PM, 16TB Capacity, External Hard Drive Reader Case Aluminum
- Compatibility: Supports 2.5 inch SATA HDD/SSD
- High-Speed Data Transfer: USB 3.1 Gen 2, 10Gbps
- Multiple RAID Modes: Supports RAID 0, 1, JBOD, PM
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Key Questions
How accurate are these size comparisons?
The comparisons are rough estimates based on standard hard drive sizes and are intended to provide a visual understanding of the data scale. Actual storage configurations vary widely.
Why do malware repositories grow so large?
Malware repositories expand due to the continuous creation of new malicious code, the collection of samples from infected systems, and the need for extensive datasets to train detection systems effectively.
What challenges do such large datasets pose?
Handling and analyzing petabyte-scale datasets require significant computational resources, advanced storage solutions, and efficient algorithms, posing ongoing technical challenges for cybersecurity teams.
Could these datasets be compressed or optimized?
While data compression can reduce storage needs, the raw size reflects the volume of unique samples. Optimization strategies are crucial but do not eliminate the fundamental scale of the repositories.









