Since 2017, a significant vulnerability in Windows, tracked as ZDI-CAN-25373, has been exploited by state-sponsored groups across the globe, putting sensitive information at risk. This flaw primarily affects Windows shortcut files (.LNK), and it’s been used predominantly for espionage and data theft. Eleven nation-state actors, including those from North Korea, China, Iran, and Russia, have leveraged this vulnerability to breach systems worldwide. About 70% of these intrusions focus on stealing information, underlining the serious implications for both individuals and organizations.
Attackers exploit the flaw by using crafted .LNK files that contain hidden command-line arguments. This allows them to execute malware without raising immediate suspicion. The complexity of detection arises from the use of Line Feed (x0A) and Carriage Return (x0D) characters, which make it difficult for security systems to identify malicious activities. Additionally, nearly 1,000 .LNK file artifacts linked to the vulnerability have been identified, highlighting the extensive nature of this exploitation.
Furthermore, the user interface misrepresentation classified as a UI issue (CWE-451) means that critical information remains obscured, giving attackers an edge in their operations. The malware delivered through this vulnerability includes notorious strains like Lumma Stealer, GuLoader, and Remcos RAT.
Notably, North Korean groups represent nearly half of those exploiting this flaw, often sharing tools and techniques among themselves. Other countries like China, Iran, and Russia also have active state-sponsored groups in this arena, with names like Evil Corp, Kimsuky, and ScarCruft making headlines for their activities.
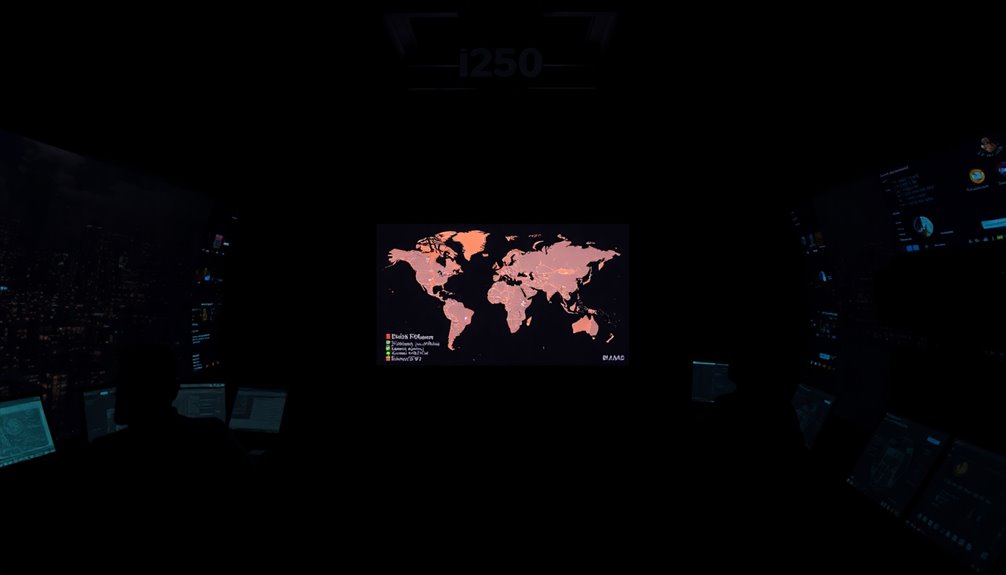
The global reach of these attacks is alarming, as they target organizations in North America, Europe, Asia, and beyond, including sensitive government agencies, financial institutions, telecommunications companies, military sectors, and energy firms.
Despite the scale of this threat, Microsoft classifies the issue as low severity and has no immediate plans for a patch. They recommend using Microsoft Defender and Smart App Control for protection while urging users to exercise caution when downloading files from unknown sources.
The lack of a decisive response from Microsoft leaves organizations exposed to significant risks of data theft and espionage. To mitigate these risks, it’s crucial for organizations to scan for malicious .LNK files and implement robust endpoint protection.









