Operation Ivy Bells was a daring Cold War mission where you, as a spy, would secretly tap into Soviet undersea communication cables to intercept crucial military and diplomatic messages. Using submarines, underwater drones, and stealth techniques, you would attach listening devices without detection. This operation demonstrated how the ocean’s depths could be exploited for intelligence, setting a precedent for future covert underwater espionage. Discover more about this daring feat and its lasting influence.
Key Takeaways
- Operation Ivy Bells was a Cold War covert mission targeting Soviet undersea communication cables using submarines and specialized tapping devices.
- The operation enabled the U.S. to intercept encrypted Soviet military and diplomatic messages silently and in real-time.
- It involved careful planning, stealth, and the use of mini-submarines, underwater drones, and night-time operations to avoid detection.
- Ivy Bells demonstrated the strategic importance of undersea cables and innovation in underwater espionage technology.
- Its success influenced future covert operations and highlighted the ocean as a crucial frontier for intelligence gathering.

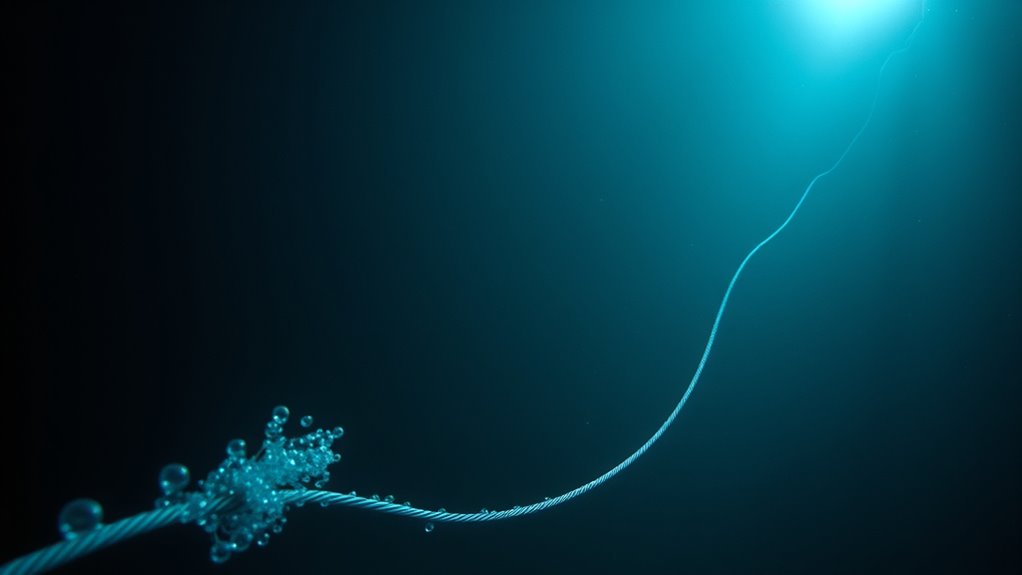
Have you ever wondered how intelligence agencies gather secrets from concealed underwater cables? During the Cold War, one of the most daring operations involved intercepting sensitive communications traveling through undersea communication cables. These cables carried critical military and diplomatic messages across oceans, making them prime targets for espionage. The operation, known as Ivy Bells, showcased the innovative spy tactics used to tap into these underwater communication lines without alerting the enemy. You can imagine the challenge: how do you secretly access a cable lying on the ocean floor, often miles from shore, and guarantee that the interception remains undetected? It required meticulous planning, cutting-edge technology, and nerves of steel.
To succeed, agents relied on a sophisticated understanding of undersea communication infrastructure. They knew that these cables were heavily guarded and often laid along predictable routes. The key was to insert a device that could intercept signals without damaging the cable or raising suspicion. Underwater communication lines are designed to be resilient, so the spy tactics involved using submarines and specialized equipment to carefully attach tapping devices. Once in place, these devices would listen in on encrypted messages, providing crucial intelligence to the United States. The operation demonstrated how espionage could extend beneath the waves, exploiting the very infrastructure that kept global communications flowing.
Executing such a covert operation demanded precision and stealth. Navy SEALs and other operatives worked in tandem, deploying mini-submarines and underwater drones to locate and attach the tap. The process involved diving deep beneath the surface, often at night, to minimize detection risk. Once the device was securely attached, the agents would retreat, leaving the tap to silently relay information for months or even years. This method of intercepting signals was revolutionary because it allowed intelligence agencies to access real-time diplomatic and military communications without physically infiltrating foreign facilities. It was a clear demonstration of how spy tactics evolved to include undersea surveillance, leveraging underwater communication systems to gain an intelligence edge during tense geopolitical conflicts.
The success of Ivy Bells highlighted the importance of undersea cable interception in Cold War espionage. It showed that the ocean’s depths weren’t just a barrier but also a battleground for information warfare. You can see how this operation set the stage for future covert activities, inspiring innovations in underwater espionage technology. Today, while the technology has advanced, the basic principle remains the same: understanding and exploiting underwater communication channels can provide a significant advantage in national security. Ivy Bells remains a legendary example of how daring and ingenuity can turn the hidden depths of the ocean into a strategic frontier for intelligence gathering.

Aquavision Underwater Drone 2026, Bionic Design/Focusing On Correction/Wireless Connectivity, Smart App Control, Real-Time Image Transmission, Suitable For Underwater Exploration
- Bionic Manta Ray Design: Sleek, durable underwater drone shape
- Surface Use Only: Not suitable for full submersion
- Enhanced Stability: Optimized weight for steady navigation
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Did Operation Ivy Bells Remain Secret for so Long?
You can see that Operation Ivy Bells stayed secret for so long because they used stealth tactics to avoid detection and kept their operations highly classified. They also relied on diplomatic cover, making it difficult for outsiders to suspect or investigate their activities. By maintaining strict secrecy and blending their actions with diplomatic or military efforts, they ensured the operation remained concealed from the public and enemy intelligence for years.
What Were the Main Technological Challenges Faced During the Mission?
You faced significant technological challenges during the mission, especially with underwater communication and cable retrieval. You had to develop stealthy equipment to avoid detection and guarantee precise handling of the delicate Soviet cables. Handling the underwater environment’s pressure and currents made cable retrieval tricky, requiring innovative tools and techniques. Maintaining silent operation while transmitting data was vital, pushing you to refine your stealth technology to succeed without alerting your adversaries.
Were There Any Similar Covert Operations During the Cold War?
Yes, during the Cold War, you can find several similar covert operations involving underwater espionage. These Cold War covert operations often involved submarines, underwater listening devices, and secret divers to gather intelligence. You might have heard of missions like the Soviet Union’s underwater cable tapping or U.S. submarine reconnaissance. These efforts aimed to intercept communications or gather strategic information, highlighting the intense underwater espionage battles that defined Cold War covert activities.
How Did the U.S. Verify the Intel Obtained From the Wiretap?
You might think the U.S. simply trusted the wiretap intel, but they didn’t. They used deception tactics to verify data, cross-checking intercepted communications with other intelligence sources. Data analysis played a essential role, helping analysts identify inconsistencies or confirm patterns that aligned with known facts. This multi-layered approach ensured they could confidently verify the intel, minimizing the risk of false information influencing critical Cold War decisions.
What Were the Long-Term Impacts of Operation Ivy Bells?
You see, Operation Ivy Bells crucially impacted Cold War espionage and technological espionage by highlighting the importance of covert operations in gathering essential intelligence. It led to increased investments in undersea surveillance and advanced communication interception techniques. This operation also set a precedent for future covert activities, shaping how nations approach espionage strategies during tense geopolitical conflicts. Its long-term influence reinforced the need for technological superiority in Cold War intelligence efforts.

Tsiodot Mini RC Submarine Waterproof Remote Control Boat Underwater Diving Fish Tank Toy for Kids Birthday Gift(Blue)
- Remote Control Submarine: Sails and dives underwater with 360° rotation
- Flexible Movement: Forward, backward, turn, dive, and surface control
- Rechargeable Battery: Built-in rechargeable battery in the submarine
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
As you reflect on Operation Ivy Bells, remember that beneath the icy waters, a tiny wire became a lifeline of secrets, symbolizing trust and danger intertwined. It’s a reminder that even the smallest actions can shift the course of history, like a ripple spreading through unseen depths. In the silent darkness, courage and caution dance together, revealing how humanity’s thirst for knowledge often hides in the shadows—where the true power lies beneath the surface.
As an affiliate, we earn on qualifying purchases.

Covert Scouting Cameras MP9 2-Pack Bundle
- Multiple Shooting Modes: 1 Shot, 3 Shot, and Video Mode
- Battery Included: Includes 8 AA batteries
- Storage Included: Includes 2 SD cards
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.