
In today's rapidly evolving digital landscape, understanding and utilizing threat intelligence isn't just beneficial—it's essential for effective cybersecurity. As a security professional, you know that threat intelligence involves analyzing data about potential or current attacks. This analysis helps you understand adversaries better and defend against them more effectively. By harnessing threat intelligence, you can proactively defend your organization and optimize your resources, ensuring that you're always one step ahead of potential threats.
The process of threat intelligence starts with data gathering. You collect data from various sources, including the open, deep, and dark web. This comprehensive approach enables you to capture a wide spectrum of threats. Once you have this data, the next step is data analysis. You analyze patterns and trends to extract actionable insights that can inform your security strategies. Additionally, effective threat intelligence feeds provide continuous streams of data related to current or potential security threats, enhancing your understanding of emerging risks.
Contextualizing these threats is equally important, as it helps you make informed security decisions tailored to your organization's unique environment. Sharing information with your security teams enhances response capabilities and strengthens your overall security posture. By integrating threat intelligence into your security tools and processes, you can streamline operations and improve alert prioritization. This integration allows your team to focus on the most relevant risks, enhancing incident response and recovery efforts.
Understanding the different types of threat intelligence is crucial, too. Strategic threat intelligence gives you a big-picture view of the threat landscape, informing high-level decision-making and resource allocation. In contrast, tactical threat intelligence offers practical, actionable information that supports your day-to-day security operations. By employing both types, you can bridge the gap between strategy and technical implementation, ensuring that your organization is well-prepared for any eventuality.
A proactive approach to threat intelligence not only anticipates and prepares for attacks but also optimizes resources effectively. With the right context about adversaries, you can enhance containment and recovery during incidents, leading to faster response times. Moreover, threat intelligence supports compliance obligations, keeping you informed about existing threats and ensuring that your organization meets regulatory requirements.

Artificial Intelligence for Cybersecurity: Develop AI approaches to solve cybersecurity problems in your organization
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
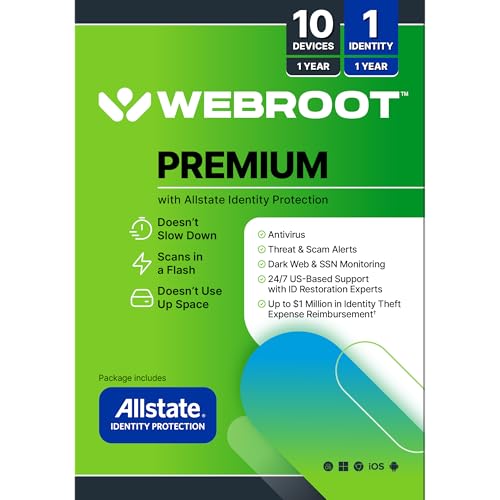
Webroot Premium 2026 with Allstate Identity Protection | 10 Device, 1 Year | Antivirus and Internet Security Software, Advanced Dark Web Monitoring, Password Manager | Packaged Version
- Device Compatibility: Protects 10 devices with cloud security
- Password Management: Securely stores and encrypts passwords
- Comprehensive Threat Protection: Defends against viruses, ransomware, phishing
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Security Information and Event Management (SIEM) Implementation (Network Pro Library)
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.









