
In an age where digital threats loom larger than ever, understanding the evolution of black bag operations is crucial. These covert entries into structures aim to gather intelligence and have a rich history, particularly within the FBI, which utilized them extensively from 1942 to the 1960s. With over 200 documented instances, the tactics involved, such as lock picking and safe cracking, set a foundation for today’s intelligence-gathering methods.
However, as the landscape shifted, so did the techniques, leading to a modern era defined by cyber espionage. The digital age has transformed espionage, integrating sophisticated tools and strategies that go beyond physical break-ins. Cyber espionage has evolved to exploit vulnerabilities in digital infrastructures, making it a significant threat to national security and highlighting the need for robust safety measures.
As espionage evolves, cyber threats now exploit digital vulnerabilities, posing significant risks to national security.
As you engage with series like *Black Bag*, you’ll notice how they depict this intersection of traditional espionage and modern cybersecurity challenges. Insights from real-life intelligence officers enrich these portrayals, providing a more authentic view of the complexities spies face today.
Despite the fascinating portrayals, it’s essential to recognize the legal ramifications surrounding black bag operations. In 1972, the U.S. Supreme Court declared these operations unconstitutional, but they’ve persisted in national security cases with the proper oversight from the Foreign Intelligence Surveillance Court. Judicial warrants are now required for criminal investigations involving black bag entries, underscoring the ongoing legal complexities.
This delicate balance between security and privacy raises questions that resonate deeply within the context of our interconnected world. As cyber threats become more prevalent, the implications for civilians and their privacy grow increasingly worrisome.
Films like Steven Soderbergh’s *Black Bag* shift the focus of the spy thriller genre, moving away from pure action towards exploring the emotional depth of espionage. By examining the character dynamics and personal struggles of spies, these narratives reveal the psychological toll of living a life steeped in secrecy and deception.
They remind you that behind every operation, there’s a human story filled with complex relationships and moral dilemmas. As you consider the implications of modern espionage, remember that real-life scenarios often inspire these fictional representations.
State-sponsored cyber operations expose the vulnerabilities of global digital systems and can have dire consequences not just for governments but for everyday people too. Engaging with these themes in the context of entertainment can provide valuable insights into the fragility of our increasingly digital world and the ongoing battle between security and privacy.
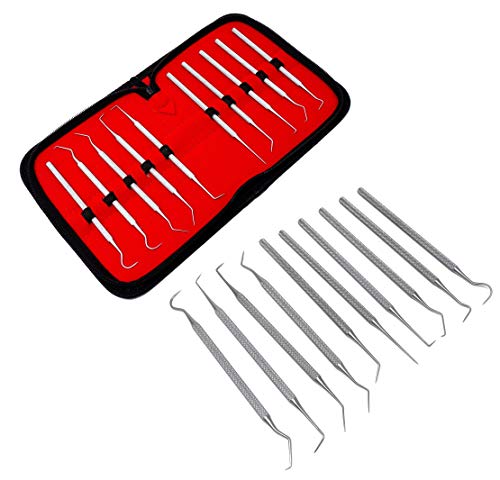
Set of 10 Stainless Steel Precision Micro Pick Set Combo, 5.5 inch to 6 inch Overall Length
- Material: Stainless Steel Points
- Precision Points: Various Tip Types Including #1, #6, #17, #23
- Handle Design: Non-Slip Handles with Six Shapes
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Locksport: A Hackers Guide to Lockpicking, Impressioning, and Safe Cracking
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Hacking Hardware: The Practical Guide to Hands-On Hardware Pentesting, Red Team Tools, and Prevention for USB, Wi-Fi, Bluetooth, RFID (Rheinwerk Computing)
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Digital Investigation Kit | Featuring iRecovery Stick, Phone Recovery Stick, Data Recovery Stick, XXX Detection Stick, Data Shredder Stick, SIM Card Seizure, Capturra Drive, Voice Logger, & More
- Device Compatibility: Investigate phones and tablets
- Data Recovery: Recover deleted data from computers
- Media Analysis: Extract and analyze photos and videos
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.









