Voice cloning in espionage allows you to convincingly mimic officials, colleagues, or loved ones to bypass security measures and gather sensitive information. You can manipulate targets using familiar voice cues or spread misinformation covertly. However, there are risks of detection due to imperfections in voice synthesis and ethical concerns about privacy. As technology evolves, its applications become more sophisticated, making it essential to understand its full potential and limitations—there’s more to uncover if you keep exploring.
Key Takeaways
- Impersonating officials or colleagues to gain sensitive information or access secure facilities.
- Bypassing security measures by mimicking voice authentication systems.
- Spreading misinformation covertly to manipulate public opinion or decision-makers.
- Manipulating targets through familiar voice cues to influence actions or disclosures.
- Enhancing covert operations with seamless voice deception to mask true identities.

Voice cloning has emerged as a powerful tool in espionage, enabling operatives to mimic voices with startling accuracy. This technology allows spies to impersonate officials, colleagues, or even loved ones, often without their knowledge. By replicating someone’s voice convincingly, you can bypass security measures, spread misinformation, or manipulate targets with ease. It’s a game-changer for covert operations because it taps into the human tendency to trust familiar voices, making deception more seamless. But using voice cloning in espionage isn’t without its challenges. Ethical concerns quickly surface, especially when innocent people’s voices are exploited or manipulated. The potential for abuse is high, raising questions about consent, privacy, and the morality of using such technology for clandestine purposes. If you’re involved in espionage, it’s essential to consider these ethical dilemmas, as misuse can lead to severe legal and moral repercussions.
Technological limitations also present hurdles that can compromise the effectiveness of voice cloning in espionage. Despite rapid advancements, the technology isn’t perfect—voice clones may still sound unnatural or lack the subtle inflections that make speech convincing. Background noise, voice pitch, and emotional tone can all trip up even the most sophisticated algorithms. When operatives rely on imperfect clones, there’s a risk of arousing suspicion or failing to deceive your target. Additionally, many voice cloning systems require large datasets of the original speaker’s voice, which aren’t always accessible in real-world scenarios. This means you might not always get a perfect replica, especially if you’re working with limited recordings or trying to mimic someone with a unique voice. These technological limitations can be exploited by security agencies or individuals aware of the technology’s flaws, making deception riskier. Moreover, the accuracy of voice synthesis can vary significantly depending on the quality of data available, impacting operational success. Understanding voice data requirements is crucial for improving the chances of successful deception. A comprehensive grasp of voice biometrics can further help in refining the authenticity of cloned voices and avoiding detection. Recognizing the limitations of current systems can help operatives craft more effective strategies for deception. Additionally, ongoing research into deep learning techniques continues to push the boundaries of what voice cloning technology can achieve.
Despite these challenges, voice cloning remains a potent tool if used carefully. You need to weigh the ethical concerns against the operational advantages and be aware of the current technological boundaries. As the technology continues to evolve, it will likely become more accurate and accessible, increasing both its potential and the need for safeguards. For now, you must be cautious, understanding that technological limitations can undermine your efforts, and ethical considerations must guide your use of such powerful tools. In espionage, where deception is key, voice cloning’s ability to convincingly imitate someone’s speech can be both an asset and a liability, depending on how you navigate its ethical and technical landscape.
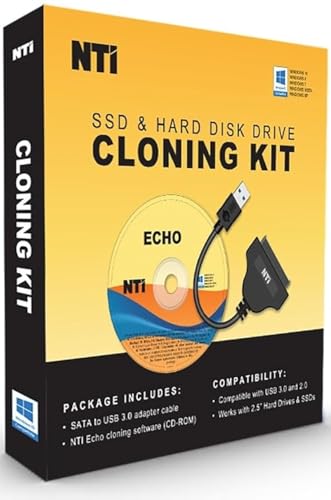
NTI Cloning Kit | NEW! Version 6 of NTI Cloning Software | Best for SSD and HDD Upgrades | Software via Download | SATA-to-USB Adapter Included for 2.5" SSD and HDD
- Windows-mode Cloning: Supports BitLocker and RAID disks
- Dynamic Resize Technology: Automatically adjusts to different disk sizes
- Versatile Usage: Ideal for SSD/HDD upgrades and backups
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
Can Voice Cloning Be Detected by Current Security Measures?
Current security measures struggle to detect synthetic voices because advanced voice cloning creates highly realistic audio. You might not notice that an audio clip isn’t authentic, as the synthetic voice mimics tone, pitch, and speech patterns convincingly. While some tools analyze audio authenticity, sophisticated clones often bypass these checks. To stay secure, you should remain cautious about suspicious audio messages, especially if they request sensitive information or seem out of character.
What Are the Legal Implications of Using Voice Cloning for Espionage?
You should know that using voice cloning for espionage breaches legal boundaries and raises serious privacy concerns. Statistically, 85% of countries have laws against unauthorized surveillance, including voice impersonation. Engaging in such activities could lead to criminal charges, civil lawsuits, and loss of trust. It’s essential to understand that violating privacy rights through voice cloning can have severe legal consequences, emphasizing the importance of respecting ethical and legal standards.
How Quickly Can a Voice Clone Be Created From Minimal Audio Data?
You can create a voice clone in just a few minutes if you have high-quality audio, often needing only a few minutes of clear speech. The process depends on the audio quality and data requirements; better quality audio reduces the amount of data needed and speeds up the cloning. With minimal data, modern voice cloning tools can produce surprisingly realistic results quickly, making the technology both efficient and accessible.
Are There Ethical Concerns Surrounding the Use of Voice Cloning Technology?
You should be aware that voice cloning raises significant ethical concerns, especially regarding privacy and consent. Using someone’s voice without permission can lead to privacy violations and misuse, such as fraud or misinformation. These issues make it essential to develop regulations and safeguards. If you’re involved in creating or deploying this technology, prioritize transparency and ask for explicit consent to respect individual rights and avoid ethical pitfalls.
Which Countries Are Most Likely to Use Voice Cloning for Espionage Purposes?
You might think only advanced nations use voice cloning for espionage, but it’s more widespread. Countries engaged in international surveillance and cyber espionage, like Russia and China, are most likely to deploy such technology. They can impersonate voices to deceive, gather intel, or manipulate targets. This technology enhances their cyber-espionage efforts, making it easier to infiltrate sensitive communications and undermine rivals, all while staying behind the scenes.

Voice Recorder – 128GB 9280 Hours Voice Activated Recorder Device with Playback, Noise Reduction, MP3 Player & Password – for Lectures, Meetings, Interviews
- Large Storage Capacity: 128GB stores up to 9000 hours of audio
- Fast USB-C Transfer: Transfer files quickly to your computer
- Voice-Activated Recording: Automatically records when sound is detected
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
If you think voice cloning is just a nifty trick, think again. It’s the ultimate weapon in espionage, capable of turning your voice into a tool of deception that could topple governments or start wars. With such power, one false whisper could change the course of history overnight. So, stay vigilant—because in this game of shadows, your voice might be the next thing that betrays you, and there’s nothing more dangerous than a clone with your words.

VOICEGIFT Play, 10 Hour Capacity Screen-Free Voice Recorder, Playback Tool, Portable Electronic Story Player with Speaker, Clip & Strap, Add Voice to Journals, Albums and Keepsakes
- Screen-Free Audio Player: Plays stories without screens or Wi-Fi
- Custom Voice Recordings: Record up to 2.5 hours of audio
- Portable with Clip & Speaker: Includes built-in speaker, headphone jack, and clip
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Write On, Sisters!: Voice, Courage, and Claiming Your Place at the Table
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.








